Setup the client certificate deployment by following this guide : https://www.virtuallyboring.com/setup-microsoft-active-directory-certificate-services-ad-cs/
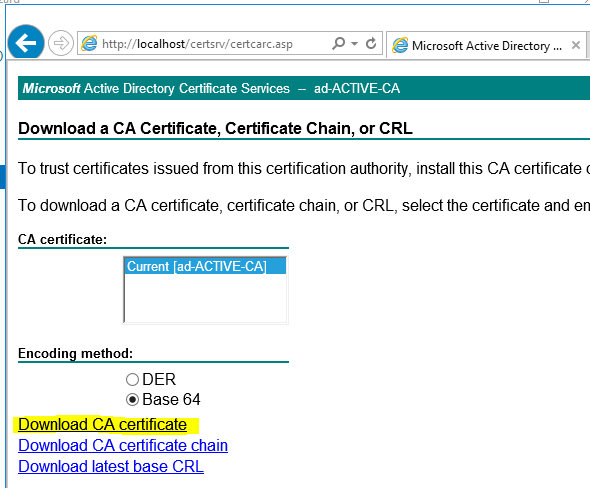
Start of by exporting the CA certificate:
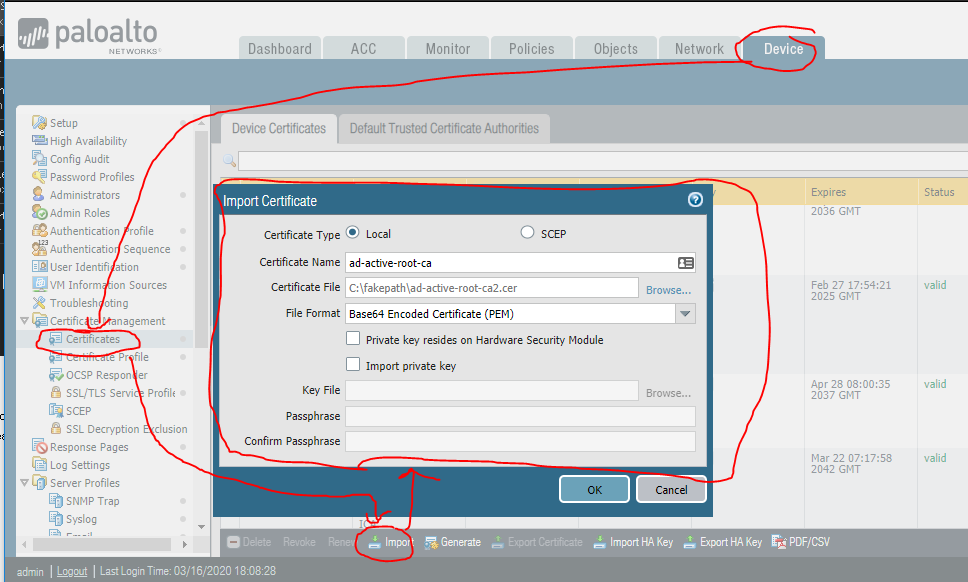
Install the certificate on you Palo Alto Firewall:
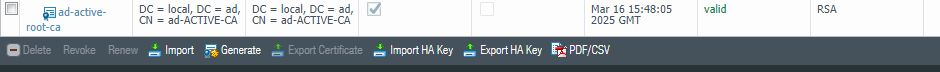
the certificate should look something like this:
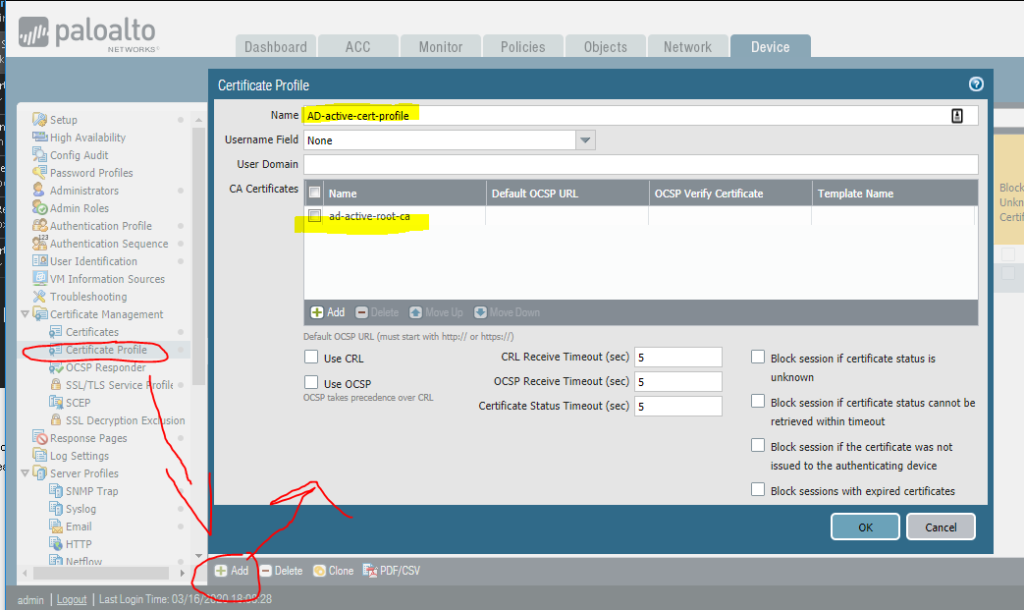
Create a Certificate profile:
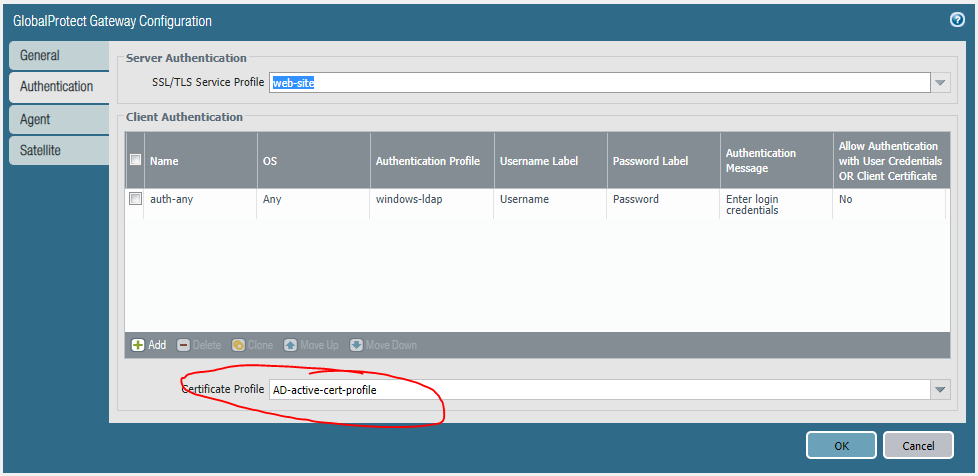
Add this profile to your Authentication settings on the GlobalProtect gateway:
Now you can access your globalprotect vpn with the required client certificate.
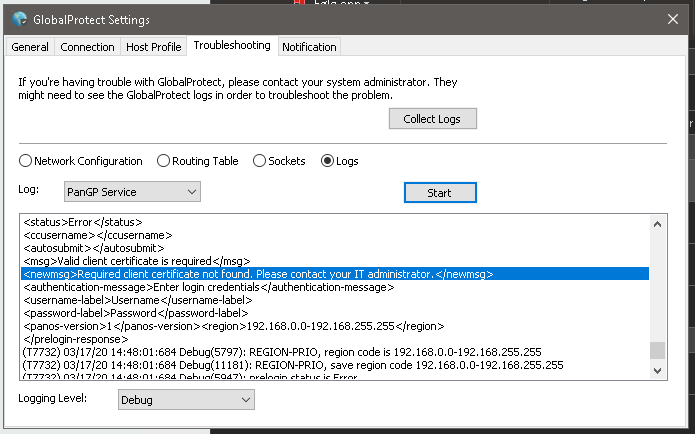
If you get disconnected right away you can check the debug logs undre Troubleshooting, look for this message: